A security researcher discovered a vulnerability in the Google Play sign-in, which lets you spy on another user’s location. While it isn’t exactly a security glitch, ill-intentioned individuals may exploit it for covert spying without the aid of stalkerware.
Google Play Sign-in can be used for covert spying!
A researcher from Malwarebytes found that someone can spy on you by simply logging in to your Google Play account. Yes, and they won’t even need to install any spyware to track the user’s real-time location.
According to the blog post, Pieter Arntz incidentally discovered this flaw when he logged into his Google play account on his wife’s phone. He then forgot to sign out from her device, and thus, started noticing unvisited locations appearing on his Google Maps Timeline. Turns out, those locations were actually coming from his wife’s phone. Initially, he speculated that it happened because he left his account signed in on his wife’s device. However, the problem persists even when he removed his account from the device.
At last, he found that Google had linked his account to his wife’s device and remained undetached even after signing out. Not just that, while he was receiving security alerts upon logging in to a new device, he noticed that his wife wasn’t getting any alerts when a new account linked to her device. This raises a big concern that users won’t even notice if a new account links to their device.
This covert tracking continued even when the researcher disabled Google time on his wife’s device. The only way you can prevent the account from tracking you is by removing the linked account manually.
A Design Feature but not a Security Flaw…
While this may result in covert spying, the vulnerability isn’t actually a security glitch. In fact, the feature is designed this way, of course, for legitimate use. But, regardless, a real-life Joe (stalker from American Netflix’s You) may find it easier to stalk someone, especially if the target user isn’t that tech-savvy.
Arntz explained in his blog post that “the vulnerability isn’t exactly a form of stalkerware, and it does not aim to disregard a user’s consent (by design). This is actually a flaw at the user’s experience end or, say, a design itself. But… it’s still a flaw and a cause of concern, especially when it enables the tracking of another person’s device.”
How can this Google Play Sign-in become a potential spyware substitute?
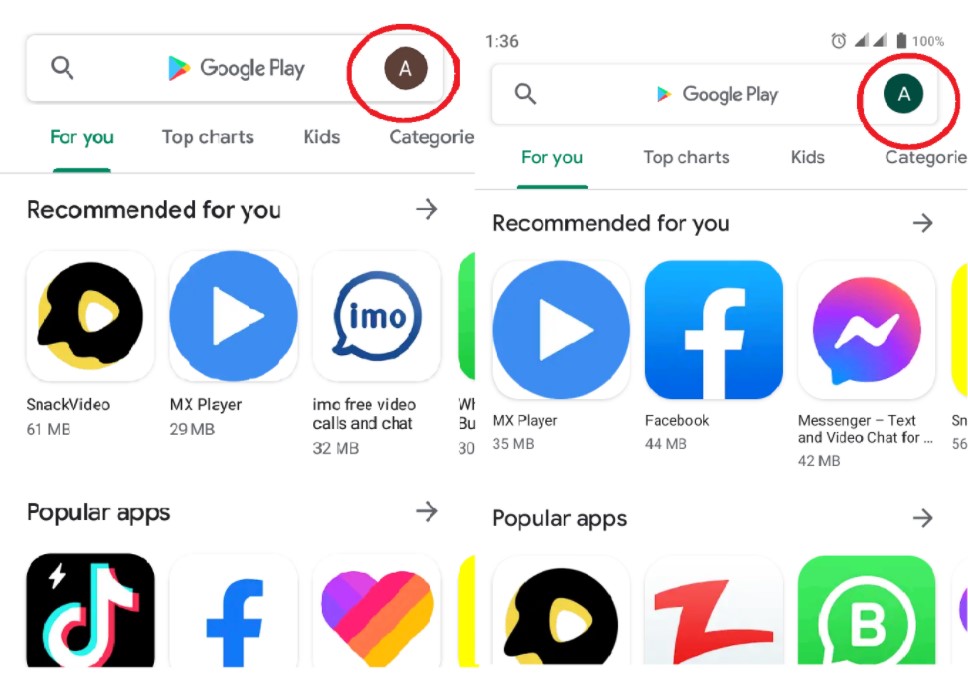
What made this feature a potential spyware alternative is the absence of any significant alert for the target user. The user remains unaware of whether their device is linked to any other Google account unless they manually check via Google account setting. This feature can even become a spying tool if a Joe in your neighborhood attempts to link an account with the same initials.
For instance, if the target users’ initials are “J,” an adversary can link an account with the same initial as “J.”
Source: latesthackingnews
And honestly, people won’t even notice it unless they had to check their accounts for another purpose. In addition, the researcher also feared that this feature can become a catalyst in domestic abuse cases. In fact, the feature can be exploited to have 24/7 surveillance over the targeted user.
And the worst part is, there are no such prominent symptoms to indicate any account link-ups. So, users must remain vigilant about this feature until Google introduces a fix for it. Meanwhile, a device restarting option can be a temporary fix to sort it out.
You can check your devices for the linked accounts using this method:
- Go to Settings
- Tap on Accounts or Accounts and Backups.
- Check if any unsolicited accounts appear in the list.
- Immediately remove the unknown account if found.
It is also advised to use a reliable VPN while using an open Wi-Fi Network. Because these networks are actually the den of cybercriminals seeking access to your device. You may get more insight in our detailed guide on why you need a VPN in Canada?
